Recap: TYPO3 Marketing Team Sprint Q4 2025
Categories:
Event Report,
Marketing
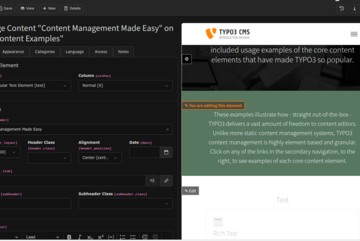
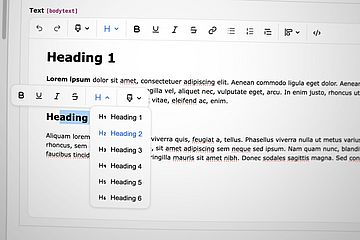
The TYPO3 Marketing Team wrapped up its final sprint of the year in Berlin on 22 October 2025. The team came together to collaborate on concepts, plans, and communication materials for TYPO3 v14, aligning on how to best present the next major release to our various audiences.
Read more