T3CON Celebrates 20 Years with ERGO by Lüftner and Parili as Patron Sponsor
Categories:
Event Report,
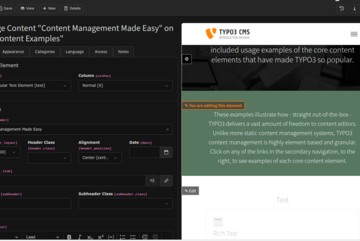
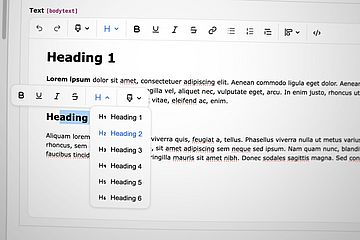
TYPO3 CMS,
Marketing
We’re pleased to announce ERGO by Lüftner and Parili as Patron Sponsor for the TYPO3 Conference 2025 (25-27 November 2025).
Read more